Bridging the Gap: Adapting a Wireshark Escher Lua Dissector for NetScout InfiniStreamNG
🔍 Introduction: The Need for Custom Protocol Visibility
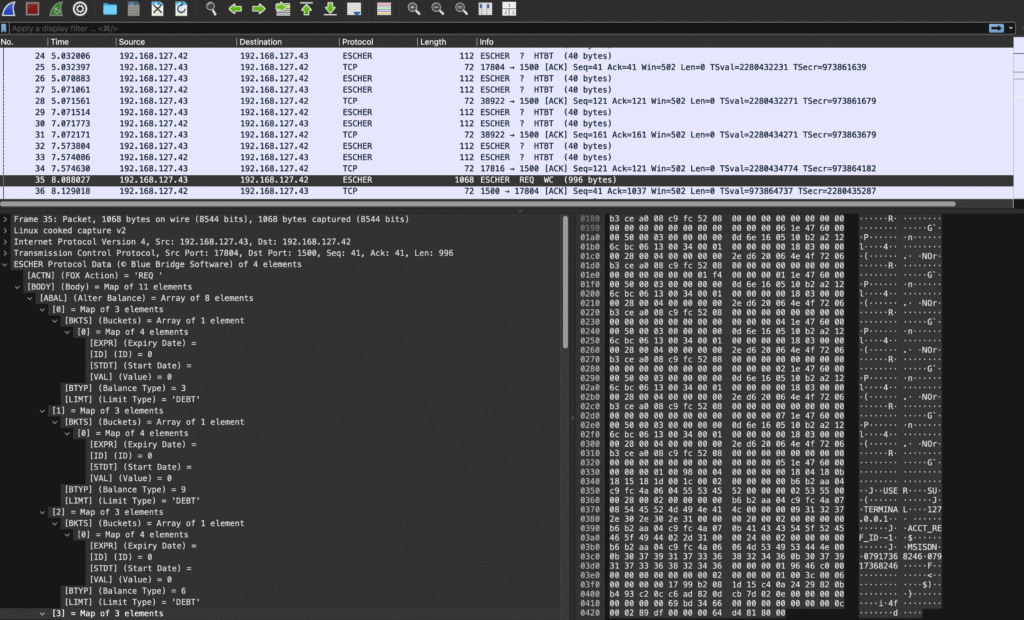
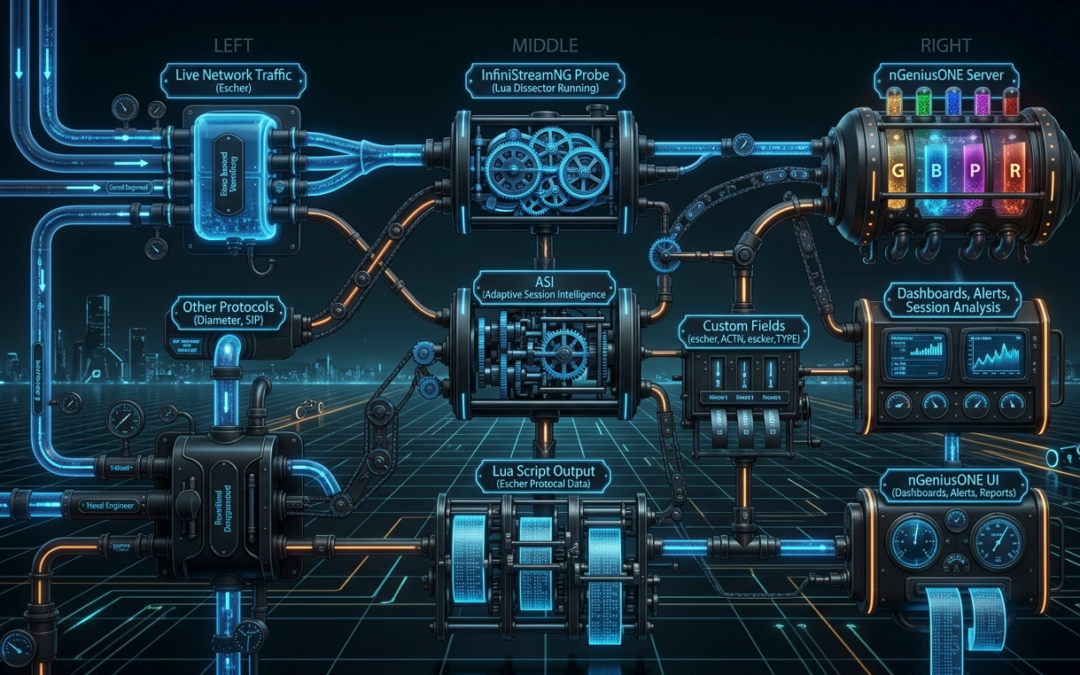
In modern telecom and enterprise networks, proprietary or niche protocols often operate under the radar of standard monitoring tools. For example, the Escher protocol, a binary protocol used in charging and session management systems, lacks native support in most commercial monitoring platforms. While my earlier Wireshark Lua dissector provided a way to decode and analyse Escher traffic offline, the real challenge was bringing this visibility into a production-grade monitoring environment like NetScout’s nGeniusONE.
This post explores how to adapt a Wireshark Lua dissector for real-time protocol dissection in NetScout InfiniStreamNG, enabling live monitoring, troubleshooting, and analytics for custom protocols within the nGeniusONE Service Assurance platform.
🌟 Why NetScout nGeniusONE?
Before diving into the technical details, it’s worth highlighting why NetScout nGeniusONE is the ideal platform for this kind of custom protocol integration. nGeniusONE is a comprehensive service assurance solution designed to provide end-to-end visibility across physical, virtual, and cloud environments. Here’s how it stands out:
📌 Key Benefits of NetScout nGeniusONE
| Feature | Benefit | Relevance to Custom Protocols |
|---|---|---|
| Real-Time Visibility | Monitors live traffic with sub-second latency, enabling immediate detection of issues. | Custom protocols like Escher can be monitored in real-time, not just post-mortem. |
| Adaptive Session Intelligence (ASI) | Uses deep packet inspection (DPI) to automatically classify and analyse traffic. | ASI can recognise standard protocols (e.g., Diameter, SIP, HTTP), while custom Lua scripts handle proprietary ones like Escher. |
| End-to-End Correlation | Correlates multi-protocol sessions (e.g., Diameter + Escher + HTTP) for holistic troubleshooting. | Enables tracking of Escher messages alongside standard protocols in a single workflow. |
| Custom Dashboards and Alerts | Create tailored dashboards and proactive alerts based on custom metrics. | Custom fields from the Escher dissector (e.g., escher.ACTN, escher.TYPE) can power real-time dashboards and alerts. |
| Scalable Architecture | Handles 10Gbps+ traffic with distributed probes (InfiniStreamNG, vSTREAM). | Lua scripts run directly on the probe, ensuring low-latency processing even at scale. |
| Historical and Trend Analysis | Stores long-term data for trend analysis, capacity planning, and forensic investigations. | Custom protocol data can be historically analysed alongside other network metrics. |
| Unified Workflow | Single pane of glass for network, application, and service-layer visibility. | Escher traffic can be seamlessly integrated with other protocols in nGeniusONE’s UI. |
| Open Extensibility | Supports custom Lua scripts for proprietary protocols and REST APIs for integration. | Enables adaptation of Wireshark dissectors and other custom logic. |
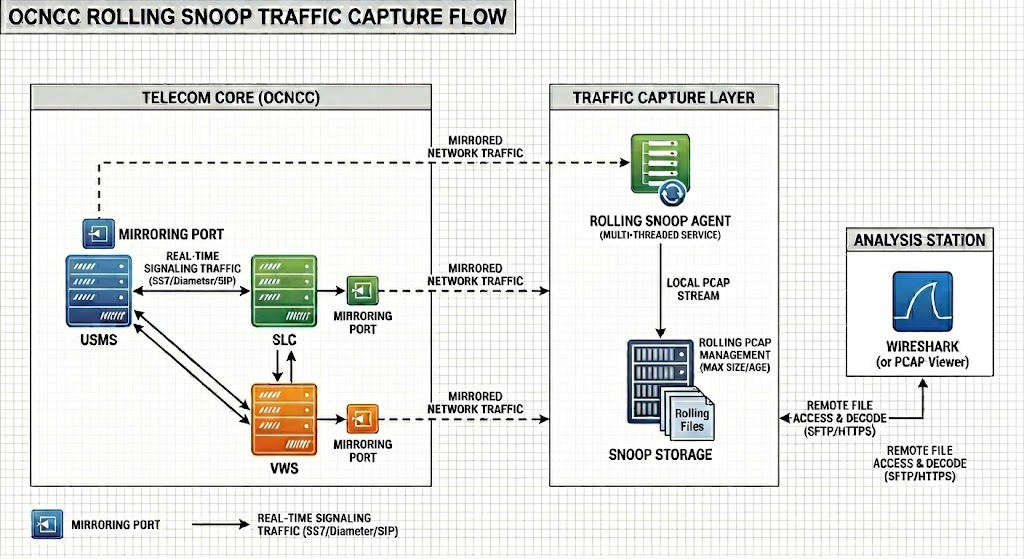
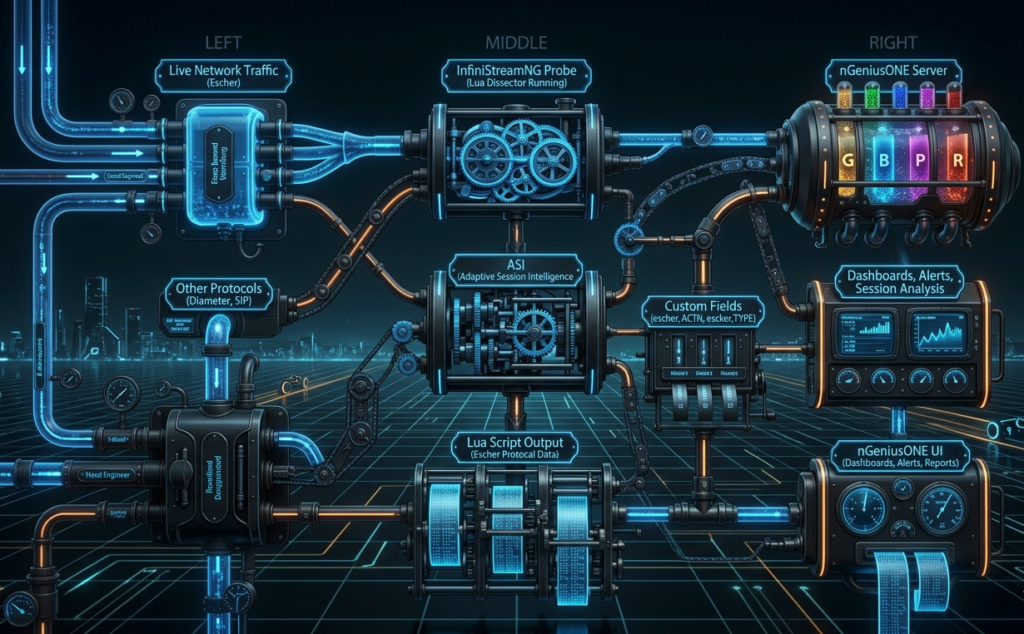
🖼️ Architecture Overview
Here’s how the custom Escher dissector fits into the nGeniusONE ecosystem:
🧩 The Challenge: From Wireshark to InfiniStreamNG
While Wireshark is an excellent tool for offline protocol analysis, it has limitations for production environments:
- No real-time processing: Wireshark dissectors run in a desktop app, not on live traffic.
- No integration with monitoring platforms: Insights from Wireshark cannot directly feed into dashboards, alerts, or automated workflows in tools like nGeniusONE.
- Manual effort: Engineers must manually capture and analyse PCAPs, which is not scalable for 24/7 operations.
NetScout InfiniStreamNG solves these issues by allowing custom Lua scripts to run directly on the probe, enabling real-time dissection of proprietary protocols like Escher.
🔧 The Adaptation Process: Key Steps
Adapting a Wireshark Lua dissector for InfiniStreamNG requires addressing fundamental differences between the two environments. Below are the critical steps and considerations:
1. Understand the Protocol Structure
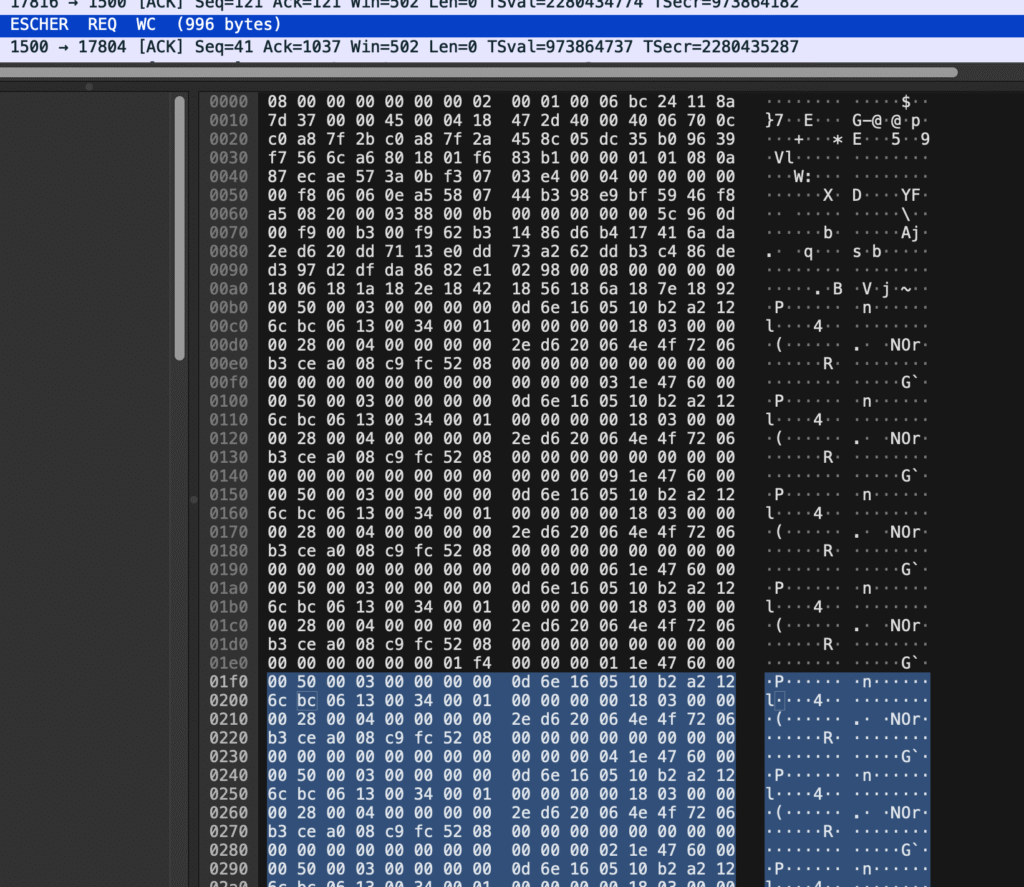
The Escher protocol uses a binary format with:
- MAPs (key-value pairs, similar to JSON objects).
- ARRAYs (ordered lists).
- Scalar types (INT32, INT64, SYMBOL, STRING, etc.).
- Nested structures (MAPs/ARRAYs can contain other MAPs/ARRAYs).
Example Escher MAP structure:
[0:2] u16 total_byte_length
[2:4] u16 num_items
[4:8] u32 internal_ptr
[8:] Index entries (4 bytes each):
bits [31:13] symbol value (19 bits, base-27 encoded)
bits [12:9] typecode (4 bits)
bits [8:0] data_offset (9 bits, in 4-byte words from MAP start)2. Replace Wireshark APIs with InfiniStreamNG Equivalents
Your Wireshark dissector relies on Wireshark’s Lua API, which is GUI-focused and not compatible with InfiniStreamNG. Here’s how to map the key functions:
| Wireshark Lua | InfiniStreamNG Lua | Example |
|---|---|---|
tvb(offset, length):uint() | payload:uint32_be(offset + 1) | local total_len = payload:uint16_be(offset + 1) (1-based indexing). |
tvb(offset, length):int64() | payload:int64_be(offset + 1) | local val = payload:int64_be(data_offset + 1) |
tree:add(proto, tvb, label) | packet:add_custom_field(name, value) | packet:add_custom_field("escher.ACTN", "REQ ") |
DissectorTable.get("tcp.port") | register_dissector(name, port, func) | register_dissector("ESCHER", 1500, dissect_escher) |
bit.band(), bit.rshift() | Same (InfiniStreamNG includes bit library). | local typecode = bit.band(bit.rshift(entry_raw, 9), 0x0F) |
3. Handle Big-Endian Fields Explicitly
InfiniStreamNG provides explicit big-endian methods for multi-byte fields. Replace all multi-byte reads with:
payload:uint16_be(offset)payload:uint32_be(offset)payload:int64_be(offset)
Example:
4. Optimise for Performance
Example:
-- Wireshark:
local total_len = tvb(offset, 2):uint()
-- InfiniStreamNG:
local total_len = payload:uint16_be(offset + 1) -- +1 for 1-based indexingInfiniStreamNG probes process millions of packets per second, so your Lua script must be highly optimised:
- Cache repeated lookups (e.g.,
FIELD_LABELS[sym_name]). - Avoid loops over large tables (e.g.,
pairs(FIELD_LABELS)). - Minimise
add_custom_fieldcalls (each call adds overhead). - Use local variables (Lua accesses locals faster than globals).
-- ❌ Slow (repeated global lookups):
for i = 0, num_items - 1 do
local sym_name = decode_symbol(payload:uint32_be(idx_off + 1))
local label = FIELD_LABELS[sym_name] or sym_name
packet:add_custom_field("escher." .. sym_name, label)
end
-- ✅ Faster (local references):
local FIELD_LABELS_LOCAL = FIELD_LABELS
for i = 0, num_items - 1 do
local sym_val = payload:uint32_be(idx_off + 1)
local sym_name = decode_symbol(sym_val)
local label = FIELD_LABELS_LOCAL[sym_name] or sym_name
packet:add_custom_field("escher." .. sym_name, label)
end5. Validate All Offsets and Lengths
InfiniStreamNG does not gracefully handle out-of-bounds buffer access. Always validate:
if offset + 4 > payload:len() then return 0 end
local total_len = payload:uint32_be(offset + 1)⚡ Performance Considerations
1. Probe Resource Usage
InfiniStreamNG probes are high-performance appliances, but Lua scripts do consume CPU and memory. Here’s what to monitor:
| Metric | Impact | Target |
|---|---|---|
| CPU Usage | Lua dissection adds ~1-5% CPU per Gbps of traffic. | Keep total Lua CPU usage <20% to avoid impacting other probe functions. |
| Memory Usage | Each Lua script consumes ~1-10MB (depends on tables like FIELD_LABELS). | Monitor with show memory in the probe CLI. |
| Latency | Aim for <1ms per packet to avoid impacting probe performance. | Test with show lua stats to measure script execution time. |
2. Optimisation Techniques
To ensure your dissector runs efficiently on InfiniStreamNG:
| Technique | Impact | Example |
|---|---|---|
| Limit Custom Fields | Reduces add_custom_field calls (each adds ~1-2μs overhead). | Only extract ACTN, TYPE, CMID (not every field). |
| Cache Lookups | Avoids repeated table accesses (e.g., FIELD_LABELS[sym_name]). | Use local variables: local FIELD_LABELS_LOCAL = FIELD_LABELS. |
| Avoid Loops | Lua loops are slow; unroll or minimise iterations. | Precompute offsets; avoid for i=1,1000. |
| Use 1-Based Indexing | InfiniStreamNG Lua uses 1-based strings (unlike Wireshark’s 0-based tvb). | payload:sub(1, 4) (not payload:sub(0, 3)). |
| Limit Recursion Depth | Prevents stack overflows in deeply nested structures. | if depth > 20 then return end. |
| Validate Offsets | Prevents crashes from malformed packets. | if offset + 4 > payload:len() then return 0 end. |
3. Testing and Validation
Lab Testing
- Deploy the script to a non-production InfiniStreamNG probe:
scp escher_dissector.lua admin@<probe_ip>:/netscout/lua_scripts/
ssh admin@<probe_ip> "lua_load escher_dissector.lua"- Replay test traffic (e.g., using
tcpreplay):
tcpreplay -i eth0 -p 1500 escher_traffic.pcap- Monitor probe performance:
- CPU:
top,htop. - Lua Errors:
tail -f /var/log/netscout/lua_errors.log. - Custom Fields: Verify in nGeniusONE (e.g.,
escher.ACTN,escher.TYPE).
- CPU:
Production Rollout
- Start with a subset of traffic (e.g., one probe, one port).
- Monitor for 24-48 hours before full deployment.
- Fallback plan: Disable the script if performance degrades:
ssh admin@<probe_ip> "lua_unload escher_dissector.lua"📈 Use Cases in nGeniusONE
Once the dissector is deployed, you can leverage the custom fields in nGeniusONE for:
1. Real-Time Dashboards
Create custom dashboards in nGeniusONE to monitor:
- Escher Message Types (e.g.,
REQ,HTBT,EXCP). - Error Rates (e.g.,
escher.ACTN == "EXCP"). - Traffic Volume (e.g., bytes/sec, messages/sec).
Example Dashboard Widgets:
| Widget | Metric | Visualisation |
|---|---|---|
| Top Escher Message Types | escher.ACTN (count by type) | Bar Chart |
| Escher Errors Over Time | escher.ACTN == "EXCP" (count) | Line Graph |
| Escher Traffic Volume | escher.map.total_len (sum) | Area Chart |
| Escher Latency | Time between REQ and RESP | Histogram |
2. Alerts and Troubleshooting
Configure proactive alerts in nGeniusONE for:
- High error rates (e.g.,
escher.ACTN == "EXCP"> 5/min). - Missing heartbeats (e.g., no
escher.TYPE == "HTBT"for 60s). - Unusual message types (e.g., unknown
escher.ACTN).
Example Alert Rule:
IF (escher.ACTN == "EXCP") AND (count > 5) THEN
trigger "Escher Error Spike" (Severity: High)
notify: Email, SMS
END3. Session Analysis
Use nGeniusONE’s Session Analyzer to:
- Track end-to-end call flows: Correlate
REQ→RESPsequences. - Link Escher to other protocols: For example, tie Escher
EXCPmessages to Diameter4010(Insufficient Funds) responses. - Drill down into individual sessions: Inspect raw Escher messages alongside Diameter/SIP.
Example Workflow:
- Filter for sessions with
escher.ACTN == "EXCP". - Drill down to see the full Escher message (including
BODYandHEADfields). - Correlate with Diameter Gy messages in the same session.
4. Historical Analysis
Leverage nGeniusONE’s historical data to:
- Trend Escher traffic over time (e.g., daily/weekly patterns).
- Identify anomalies (e.g., spikes in
EXCPmessages). - Compare with other protocols (e.g., Escher vs. Diameter latency).
Example Historical Report:
- Escher Traffic Trends: Messages/sec over the last 30 days.
- Error Correlation: Compare
escher.ACTN == "EXCP"with DiameterResult-Code == 4010.
🔗 Resources and Further Reading
- NetScout InfiniStreamNG Documentation – Official docs for InfiniStreamNG probes.
- NetScout nGeniusONE Product Page – Overview of nGeniusONE’s features and benefits.
- Wireshark Lua Dissector Reference – For understanding the original dissector logic.
- NetScout ASI (Adaptive Session Intelligence) – How ASI automatically classifies traffic.
- GitHub: Lua Performance Tips – General Lua optimisation advice.
🚀 Conclusion: Unlocking Full Visibility with Custom Dissectors
Adapting a Wireshark Lua dissector for NetScout InfiniStreamNG bridges the gap between offline analysis and real-time monitoring. By leveraging InfiniStreamNG’s Lua scripting capabilities, you can:
✅ Monitor proprietary protocols (like Escher) in real-time.
✅ Integrate with nGeniusONE for dashboards, alerts, and troubleshooting.
✅ Gain end-to-end visibility into custom and standard protocols in a single pane of glass.
While the adaptation process requires careful attention to performance and API differences, the payoff is production-grade visibility into previously opaque traffic. This approach is not just for Escher, it can be applied to any custom protocol in your network, unlocking new levels of observability and control.
Have you adapted a Wireshark dissector for InfiniStreamNG or another monitoring tool? Share your experiences!
Author Bio
Tony Craven is a telecom and network solutions architect with over 20 years of experience in Oracle Communications Network Charging and Control (OCNCC) and real-time protocol analysis. He is a strategic technology executive with proven leadership in telecommunications, IoT, and SaaS, specialising in scalable, cloud-based solutions for global enterprises and startups. Adept at bridging vision and execution, from post-merger technical integration to architecting high-availability infrastructure supporting millions of IoT devices.